KYRA MDR — AI-Powered Managed Detection & Response Platform with SIEM, NDR, EASM
_ __ __ __ ____ _ __ __ ____ ____ | |/ / \ \ / / | _ \ / \ | \/ | _ \| _ \ | ' / \ V / | |_) | / _ \ | |\/| | | | | |_) | | . \ | | | _ < / ___ \ | | | | |_| | _ < |_|\_\ |_| |_| \_\/_/ \_\ |_| |_|____/|_| \_\
$ cat /etc/kyra/mission.conf
# Managed Detection & Response Platform
# Real-time threat detection, automated response,
# and continuous threat hunting for enterprise environments.
$ kyra --status
$ _
# AI-Powered MDR Automation
$ kyra ai --capabilities
AI Alert Triage
LLM-powered alert analysis filters 99% of false positives — only real threats reach analysts
Auto-Correlation Engine
Clusters related alerts across sources into unified incidents using graph-based entity linking
AI Threat Hunting
Continuously scans telemetry for hidden attack patterns and zero-day indicators using behavioral models
Incident Summarization
Auto-generates executive summaries, root cause analysis, and remediation steps for every incident
$ kyra automation --show-pipeline
Ingest AI Analysis Decision Action
====== =========== ======== ======
[Log Stream ] --> [Normalize ] --> [AI Triage ] --> [Auto-Close FP ]
[EDR Alerts ] --> [Enrich ] --> [Risk Score ] --> [Escalate P1-P2 ]
[NDR Events ] --> [Correlate ] --> [MITRE Map ] --> [Run Playbook ]
[Cloud Logs ] --> [Deduplicate ] --> [Predict Next ] --> [Contain + Notify]
Throughput: 50K EPS ~200ms ~500ms ~30s to action
| false_positive_reduction | 99.1% |
| mean_time_to_detect | < 30 sec |
| mean_time_to_respond | < 5 min |
| auto_resolution_rate | 78% |
| mitre_technique_coverage | 200+ techniques |
| event_throughput | 50,000 EPS |
# AI models fine-tuned on Korean threat landscape and APT groups
# Human-in-the-loop for critical severity — full auto for known patterns
$ kyra ai --feature-matrix
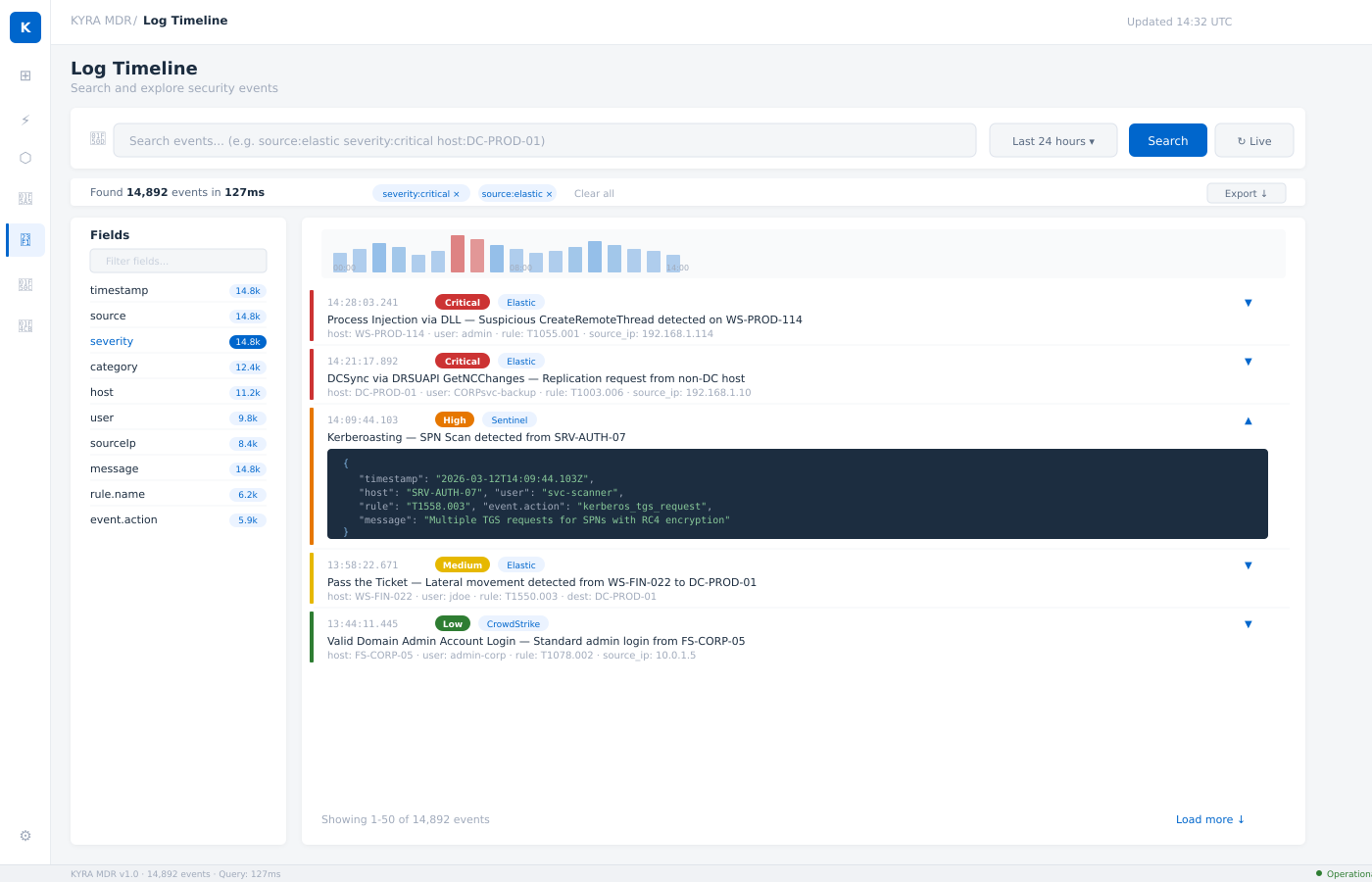
| natural_language_query | Ask questions in plain language — AI translates to log queries |
| anomaly_detection | Baseline learning + statistical deviation alerts per entity |
| ueba_scoring | User & entity behavior analytics with risk score timeline |
| predictive_defense | Predicts likely next attacker actions based on MITRE kill chain |
| adaptive_playbooks | Playbooks that self-adjust response steps based on context |
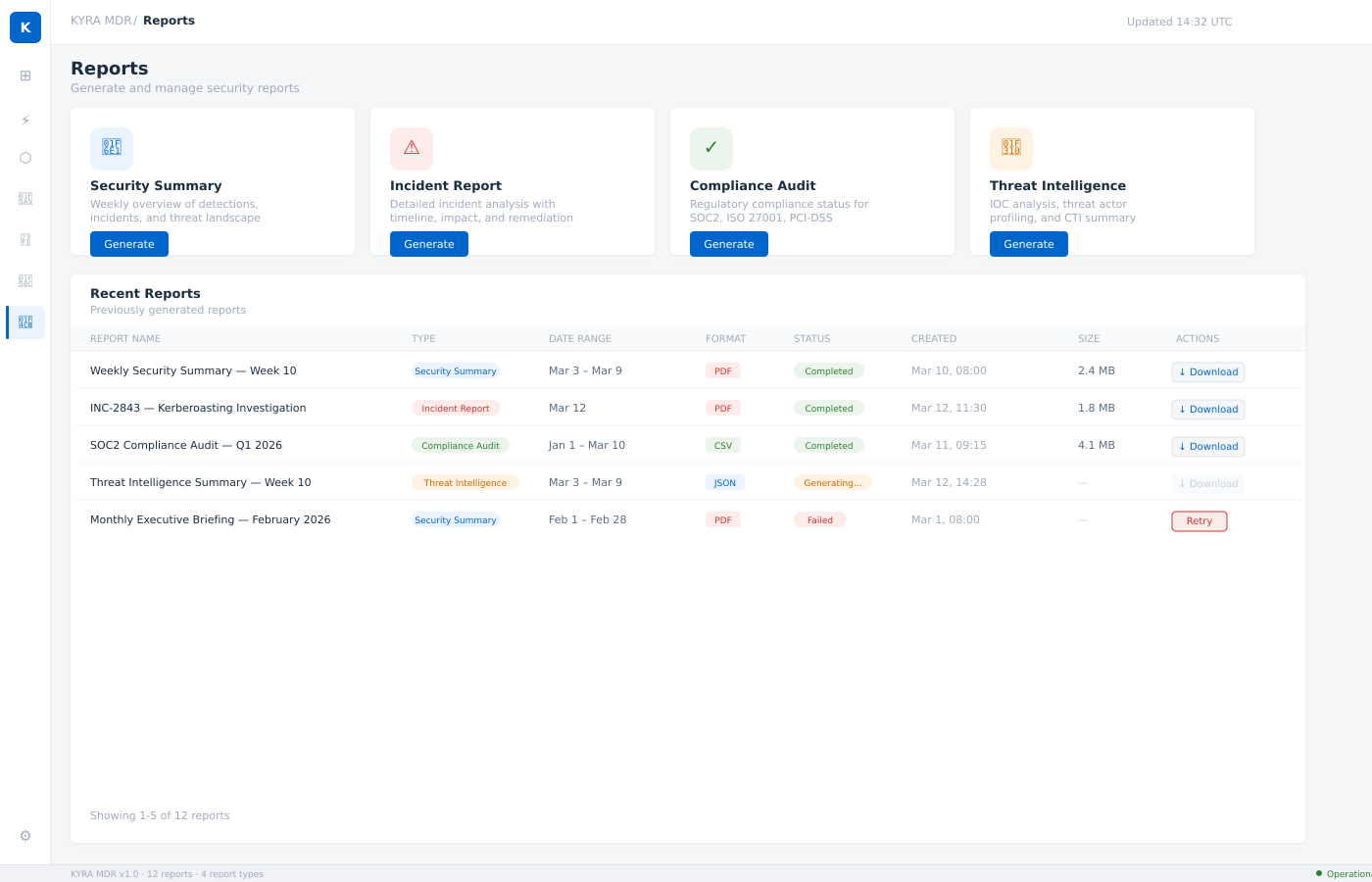
| auto_reporting | Generate compliance reports, executive briefs, and board decks |
# All AI outputs include confidence scores and explainability traces
# See It In Action
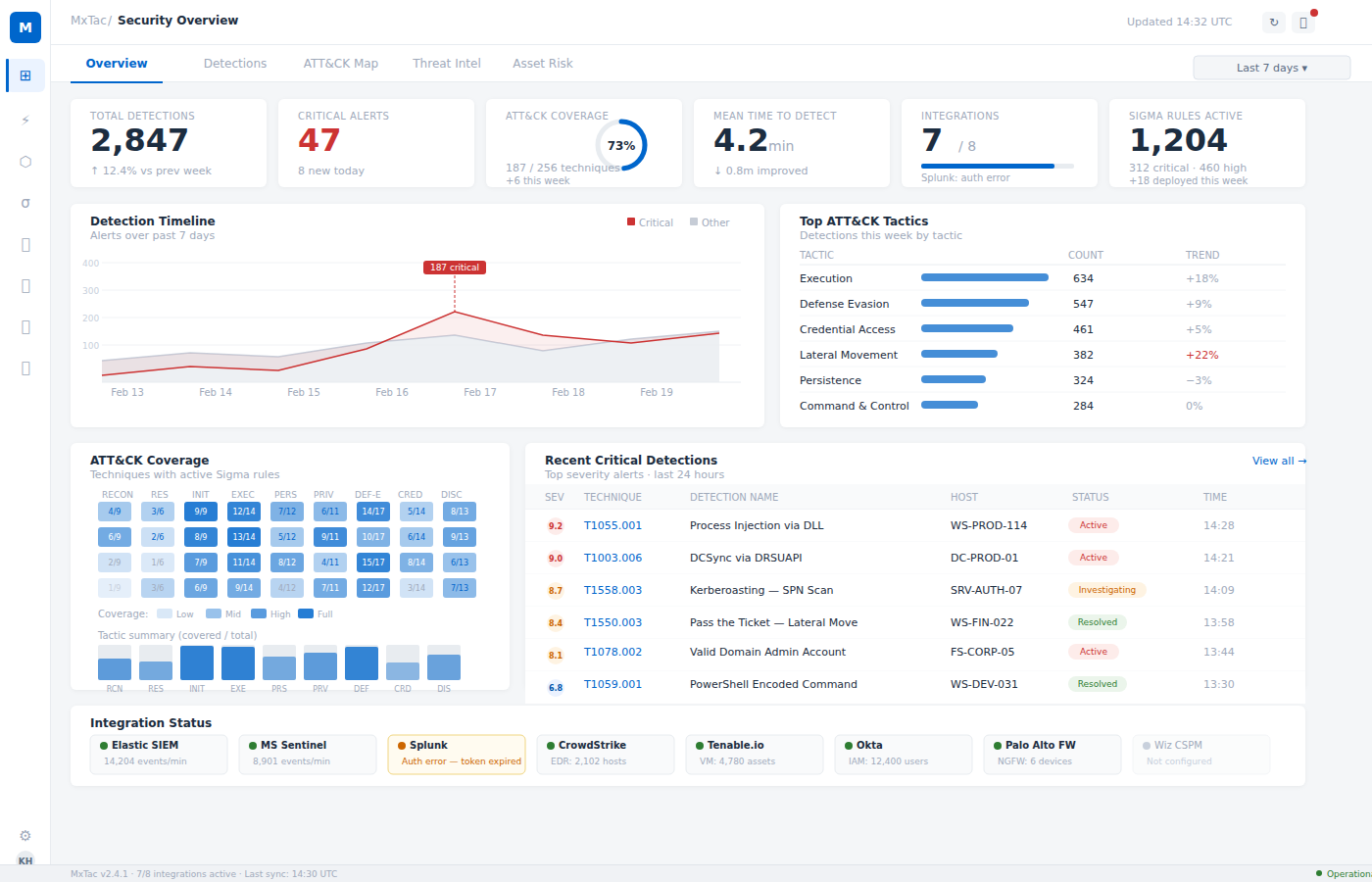
Enterprise-grade security operations console with real-time threat visibility
# Platform Overview
$ kyra describe platform
KYRA MDR is an AI-powered Managed Detection & Response platform
designed for enterprise SOC teams. Built on open standards with
full MITRE ATT&CK mapping, Sigma rule engine, and automated
response orchestration.
kyra-mdr-platform/
|
+-- detection-engine/ # Sigma rules, behavioral analytics, ML models
+-- response-engine/ # SOAR playbooks, automated containment
+-- threat-intel/ # OTX, AbuseIPDB, custom feeds
+-- siem-pipeline/ # Log ingestion, normalization, enrichment
+-- ndr-engine/ # Network traffic analysis, DPI
+-- identity-analytics/ # UEBA, impossible travel, privilege escalation
+-- compliance/ # ISMS-P, ISO 27001, SOC 2, TISAX, CMMC, CCPA
+-- tenant-portal/ # Multi-tenant dashboard, RBAC, SSO
| multi_tenant | true | # Full tenant isolation with RBAC |
| deployment | SaaS / On-Prem / Hybrid | # Flexible deployment models |
| retention | 90-365 days | # Configurable per plan |
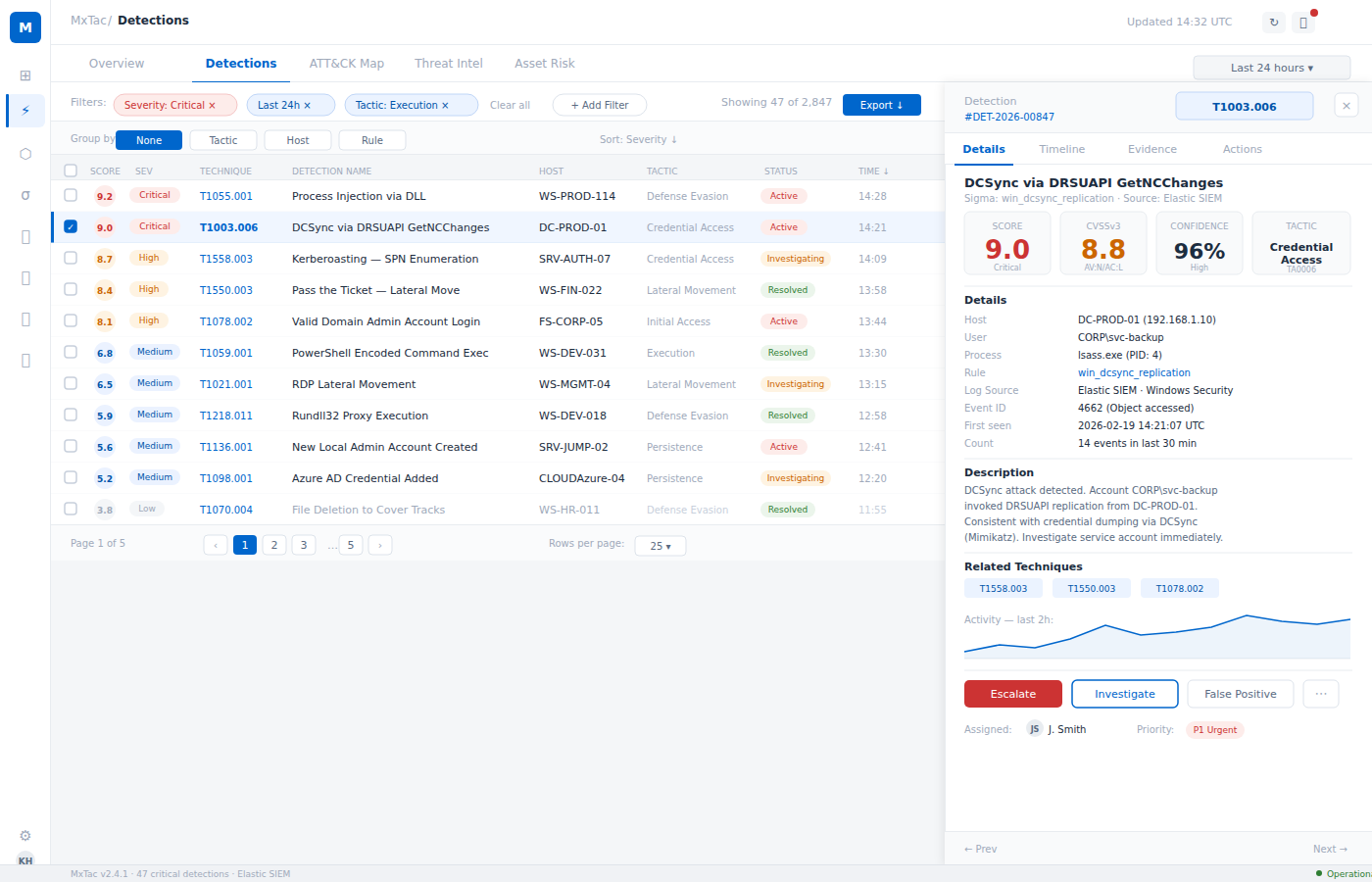
# Detection Engine
$ kyra rules --stats
Sigma Rule Engine v3.2
===========================
# Custom rule authoring supported via YAML DSL
# Auto-mapped to MITRE ATT&CK technique IDs
$ kyra mitre --matrix
█ covered █ partial
# 14 tactics / 200+ techniques mapped
$ kyra detect --list-methods
[01] Sigma Rule Correlation
Pattern-based detection using 3,200+ Sigma rules.
Multi-source log correlation across endpoints,
network, identity, and cloud telemetry.
[02] Behavioral Analytics (UEBA)
Baseline user/entity behavior profiling.
Anomaly scoring for impossible travel,
privilege abuse, and lateral movement.
[03] Network Traffic Analysis
Deep packet inspection, JA3/JA3S fingerprinting,
DNS anomaly detection, encrypted traffic
analysis, and C2 beacon identification.
[04] Threat Intelligence Correlation
Real-time IOC matching against OTX, AbuseIPDB,
and custom threat feeds. STIX/TAXII ingestion
with automated enrichment pipeline.
# Response & Automation
$ kyra playbook --describe incident-response
Detection Triage Response Remediation
========= ====== ======== ===========
[Sigma Rule] ---> [Severity ] --> [Auto-Contain ] --> [IOC Block ]
[UEBA Alert] ---> [Scoring ] --> [Isolate Host ] --> [Patch Deploy ]
[NDR Alert ] ---> [Correlation ] --> [Kill Process ] --> [Cred Reset ]
[TI Match ] ---> [Dedup ] --> [Notify SOC ] --> [Forensic Pkg ]
[Enrich ] --> [Create Ticket ] --> [Post-Incident]
Timeline: ~30s ~2min ~5min ~30min
$ kyra playbook --list
| malware_containment | Isolate + kill + scan + restore |
| credential_compromise | Disable account + force MFA + audit trail |
| lateral_movement | Segment + block + trace + report |
| data_exfiltration | Block egress + snapshot + forensics |
| ransomware_response | Isolate + backup verify + decrypt assess |
| insider_threat | Monitor + restrict + legal escalation |
| phishing_response | Quarantine + URL block + user notify |
| brute_force | Rate limit + IP block + lockout policy |
# Custom playbooks via YAML workflow DSL
# Approval gates configurable per severity level
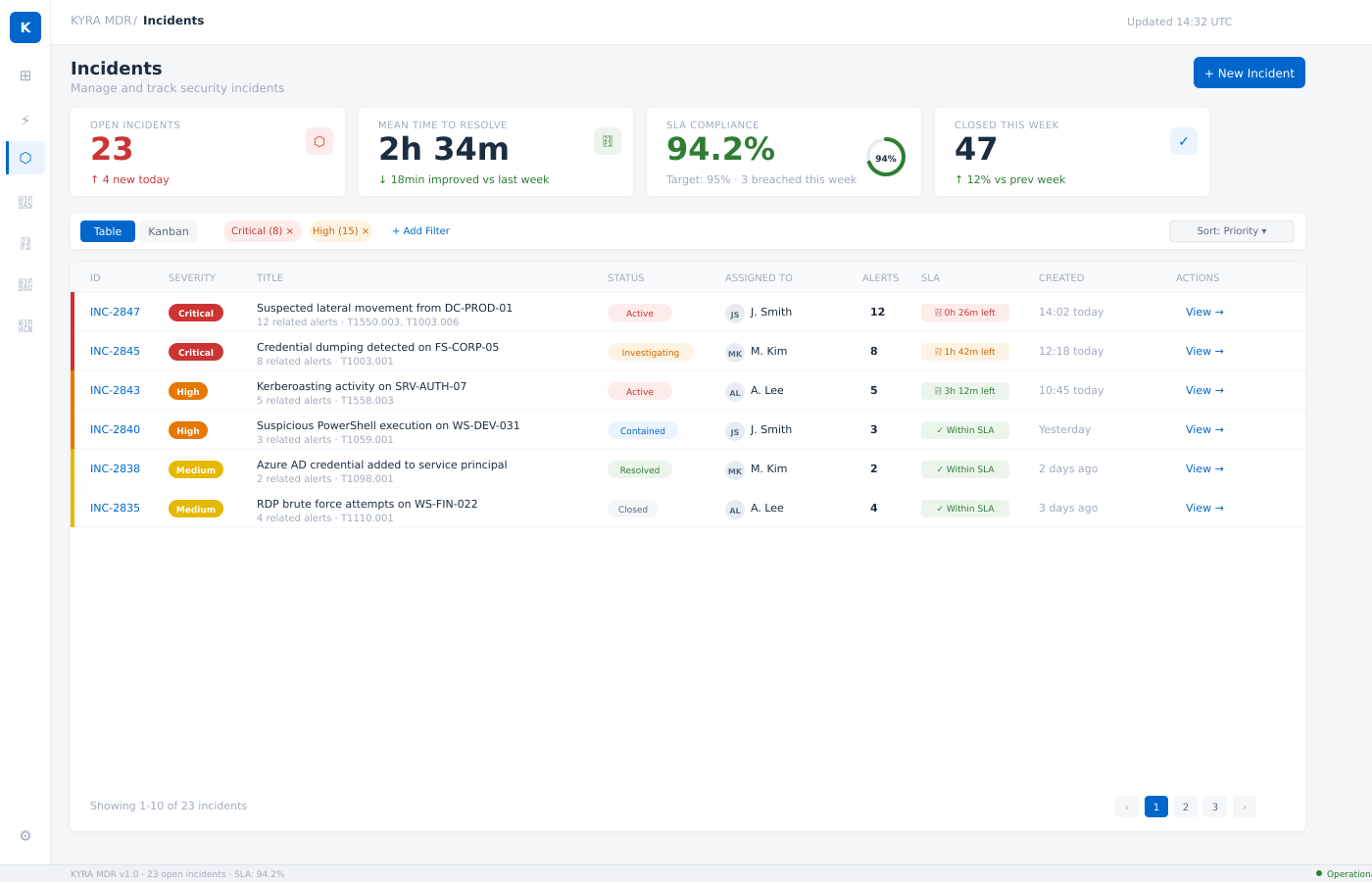
$ kyra incident --capabilities
Incident Timeline
Unified event timeline with log, alert, and action correlation
Task Assignment
Break incidents into tasks, assign to analysts, track SLA
Evidence Collection
Automated forensic artifact packaging and chain-of-custody
Post-Incident Review
Automated timeline report with MITRE mapping and IOC export
# Architecture
$ kyra arch --diagram
+-------------------+
| Tenant Portal |
| (Web Console) |
+--------+----------+
|
+--------v----------+
| API Gateway |
| (Auth, Routing) |
+--+-----+------+--+
| | |
+------------+ +--+--+ ++-----------+
| | | |
+--------v------+ +-----v---+ +-------v------+ |
| Detection Svc | | SIEM | | Admin API | |
| (Sigma,YARA) | | Pipeline| | (Billing, | |
+--------+------+ +-----+---+ | Tenant Mgmt) | |
| | +--------------+ |
| +-----v---------+ |
| | Event Bus | +-------v-------+
| | (Streaming) | | Notification |
| +-----+---------+ | Svc (Email, |
| | | Slack, SMS) |
+--------v------+ +----v--------+ +---------------+
| Threat Intel | | Analytics |
| (OTX,AbuseIP) | | Engine |
+---------------+ +----+--------+
|
+-------v--------+
| Platform DB |
| (Multi-tenant)|
+-------+--------+
|
+-------v--------+
| Cache Layer |
+----------------+
$ kyra arch --stack
| portal | Web-based tenant console, real-time dashboards |
| api | RESTful API gateway, WebSocket event streaming |
| database | Multi-tenant with row-level security (RLS) |
| analytics | High-cardinality columnar log analytics engine |
| cache | In-memory cache (session, rate-limit, threat-intel) |
| messaging | Distributed event streaming, log pipeline |
| search | Full-text log search, NDR event indexing |
| auth | JWT + OAuth2 / SAML SSO / MFA (TOTP) |
| encryption | AES-256-GCM (at rest), TLS 1.3 (in transit) |
$ kyra pipeline --describe
Agents/Syslog/API Normalization Detection Storage
================== ============= ========= =======
[Endpoint Agent ]--+
[Syslog (CEF) ]--+--> [Parse ] --> [Enrich ] --> [Sigma ] --> [Platform DB ]
[Cloud API ]--+ [Normalize] [GeoIP ] [UEBA ] [Analytics ]
[Network Sensor ]--+ [Validate ] [TI-IOC ] [ML Model] [Search Index]
[Identity (AD) ]--+
Throughput: 50,000 EPS per node | Latency: < 500ms end-to-end
# Integrations
$ kyra connector --list-supported
// Endpoint Detection & Response (EDR)
// SIEM & Log Sources
// Cloud Security
// Network & Firewall
// Identity & Access
// Ticketing & Communication
| protocol | REST API / Syslog / Event Stream / S3 / Webhook |
| format | JSON / CEF / LEEF / CSV / STIX / TAXII |
| custom | Custom connector SDK (Python/Go) |
# Pricing
★ LAUNCH EVENT — 연간결제 50% 할인 (1년간 한정)
FREE
₩0
Basic monitoring
+ 1 log source
+ 500 MB daily ingestion
+ 7-day retention
+ AI alert summary
+ Monthly EASM scan
+ Read-only dashboard
- Auto-response
- Threat hunting
MDR
₩300,000/mo
₩3,600,000 → ₩1,800,000/yr
Full AI MDR + SIEM + EASM
+ Unlimited log sources
+ 5 GB daily ingestion
+ 90-day retention
+ AI triage (99% FP filter)
+ Standard SOAR playbooks
+ Weekly EASM scan
+ Email support (24hr)
- Threat hunting
PRO
₩800,000~/mo
+ Analyst + compliance
+ Everything in MDR
+ 20 GB daily ingestion
+ 180-day retention
+ Custom SOAR playbooks
+ Monthly threat hunting
+ Shared analyst
+ ISMS-P + SOC 2
+ Dedicated support (4hr)
CUSTOM
Contact us
Enterprise-grade
+ Everything in PRO
+ Unlimited ingestion
+ 1yr+ retention
+ Weekly threat hunting
+ Named analyst
+ Multi-framework compliance
+ Dedicated support (1hr)
+ On-site onboarding
# ★ Launch event: 연간결제 시 50% 할인 적용 (출시 후 1년간 한정)
$ kyra billing --ndr-addon
# Smart traffic reduction: metadata-only analysis + adaptive sampling
# Typical 85-95% bandwidth reduction vs full-packet capture NDR
| tier | Price | Traffic | Includes |
| MDR | ₩150,000/interface/mo | ≤ 1 Gbps | Flow metadata, DPI (8 proto), JA4, 13 ATT&CK rules |
| Pro | ₩250,000/interface/mo | ≤ 10 Gbps | + behavioral baseline, IOC matching, daily analyst review |
| Custom | Negotiated | 10 Gbps+ | Unlimited interfaces, full PCAP on-demand, dedicated tuning, on-site installation |
# How traffic reduction works:
+ Metadata-only transport — headers + flow records, not full packets
+ Adaptive sampling — 1:100 for normal traffic, full capture on anomaly
+ Edge pre-filtering — drop known-good (Windows Update, CDN) at collector
+ Protocol-aware compression — deduplicate DNS/TLS/HTTP headers
+ On-demand PCAP — full packet capture triggered only on alert escalation
# NDR runs on the existing collector agent — no additional hardware.
# TAP/SPAN port connection only. Volume does NOT count toward SIEM log limits.
# Annual billing: 2 months free (₩1,500,000 → ₩1,250,000/interface/yr for MDR).
$ kyra compliance --supported
ISMS-P
Korean information security management
ISO 27001
International security standard
SOC 2
Service organization controls
PCI-DSS
Payment card industry security
TISAX
Automotive information security
CMMC
Cybersecurity Maturity Model Certification
GDPR
EU data protection regulation
CCPA
California consumer privacy act
NIST CSF
Cybersecurity framework
# Automated evidence collection and audit trail
# Scheduled compliance reports (PDF/CSV)
# Real-time compliance posture dashboard
# Get Started Free
$ kyra account --create